 sadly I couldn´t join the Avaya ATF Europe event this year that was taking place in Dublin 10th to 13th of May 2016. Thanks to the networking infrastructure forum member OfWolfAndMan who provided me the presentations of the ATF event. Many thanks for that. Avaya has come up with some interesting news , here are some points that looked interesting for me.
sadly I couldn´t join the Avaya ATF Europe event this year that was taking place in Dublin 10th to 13th of May 2016. Thanks to the networking infrastructure forum member OfWolfAndMan who provided me the presentations of the ATF event. Many thanks for that. Avaya has come up with some interesting news , here are some points that looked interesting for me.
Hardware
Avaya has introduced the ERS4900 device family witch is the successor to the ERS4800 devices. Like in the VSP family the ERS4900 will share the same software code with the ERS5900 series. That make sense to me instead of developping multiple BOSS images you have a shared code base. That model has worked out great in the VSP family and gives also the nice benefit of feature parity from a code standpoint.
The VSP7200 is now available as a licensed 24port version. You will get the 48 Port hardware of the VSP7200 that is limited to 24 ports. For me that looks like the replacement for the VSP7000 that should be named ERS7000 because it was running the BOSS image. It had also the limitation that you couldn´t run L3 routing and SPB in parallel. The only caveat that I see here is that with the VSP7200 you loose the stacking capability.
Software
On the Software side the two new exciting features for me are DVR Distributed Virtual Routing and Port Mirroring for the SPB Fabric. DVR will bring the capability to run the L3 distributed across multiple Access Switches in a SPB fabric. With that you can go full L3 on the Top of The Rack Switches and eliminating the need that packets have to sent to a centralized L3 Gateway. It is addressing the fist hop redundancy and the L3 load balancing problem at the same time. So traffic that is needed to be routed between two devices that are connected on the same Access switch can now be routed locally on that device.
Port mirroring across the fabric is the other new feature that cached my attention. Often it was a problem on traditional networks to do port mirroring. With the capability to send the Mirrored port traffic to an ISID in the SPB fabric you can transport it to any access port in the fabric. That brings a lot of flexibility. It is also possible to send multiple port mirrors to one ISID or to have multiple receivers. That gives you everything you would like to have in TAB network. Because SPB brings native multicast support this is something that can run in the background and fits natively into the fabric.
If you want to know more about it listen to the Network Braodcast Storm Podcast Episode 06 in that we had a nice conversation about DVR and Port Mirroring for SPB fabrics with Roger Lapuh from Avaya.
 I am facing a strange problem with the Firepower management center 4000 (FMC) that was formaly known as Firesight Management Center. Cisco recently release SW code 6.1 for the FMC. With SW 6.1 the 10 Gig interface have become avaialble. The 10 Gig ports have been there in hardware but you couldn´t use them with the previous software releases.
I am facing a strange problem with the Firepower management center 4000 (FMC) that was formaly known as Firesight Management Center. Cisco recently release SW code 6.1 for the FMC. With SW 6.1 the 10 Gig interface have become avaialble. The 10 Gig ports have been there in hardware but you couldn´t use them with the previous software releases.
 sadly I couldn´t join the Avaya ATF Europe event this year that was taking place in Dublin 10th to 13th of May 2016. Thanks to the networking infrastructure forum member OfWolfAndMan who provided me the presentations of the ATF event. Many thanks for that. Avaya has come up with some interesting news , here are some points that looked interesting for me.
sadly I couldn´t join the Avaya ATF Europe event this year that was taking place in Dublin 10th to 13th of May 2016. Thanks to the networking infrastructure forum member OfWolfAndMan who provided me the presentations of the ATF event. Many thanks for that. Avaya has come up with some interesting news , here are some points that looked interesting for me.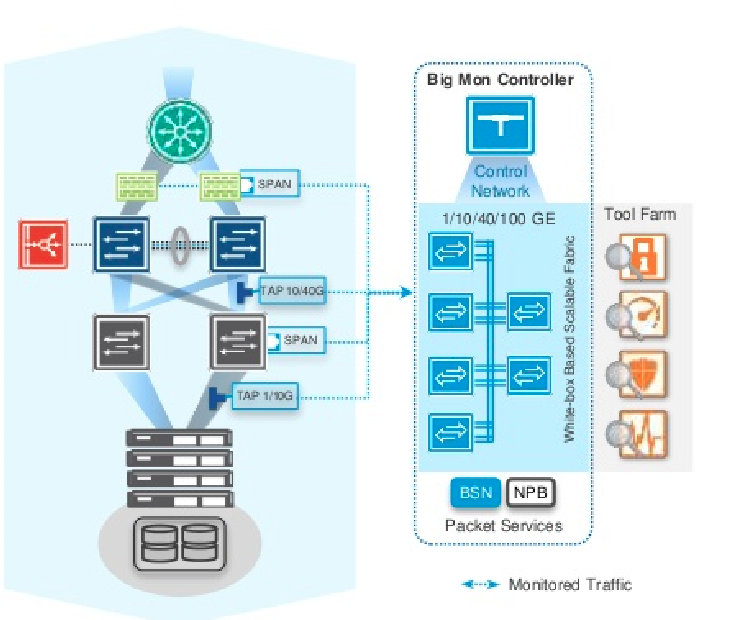 ect a datacenter it is very commen to use a set of tools or Tool Farm with a varity of different technolgies like FlowAnalyzer, IDS, IPS, ect. All of them will need to have a copy of the actual traffic that is going across the Links of your datacenter. With only one tool you could get away with a standard span/monitoring port , but when you are using multiple tools and would like to see the traffic on different links like e.g. inside and outside of your firewall, you need an extra dedicated TAB Network that can deliver you the different monitored sources for your toolfarm. If you have deployed that you know “where to find the rainbow in your network”. That was done in the past with special hardware or TABs. The approach from the Big Switch Monitoring Fabric is to use standard whitebox switches for that with the BigSwitch Software on top. With the software based appoach you get a much more flexible TabNetwork that can be programmed via API and is capbale of Event triggered Monitoring. That wouldn´t be possible with only switches. BigSwitch introduced a new component witch they call Service Node. It is a x86 based server that uses DPDK in the backround to do all the magic that can not be proceded by a switch. The Big Monitoring Fabric is the first product that uses the Service node but I suggest in the Future all the really exciting new stuff from BigSwitch will be done with some kind of x86 servers that have more flexebilty from a software capability standpoint.
ect a datacenter it is very commen to use a set of tools or Tool Farm with a varity of different technolgies like FlowAnalyzer, IDS, IPS, ect. All of them will need to have a copy of the actual traffic that is going across the Links of your datacenter. With only one tool you could get away with a standard span/monitoring port , but when you are using multiple tools and would like to see the traffic on different links like e.g. inside and outside of your firewall, you need an extra dedicated TAB Network that can deliver you the different monitored sources for your toolfarm. If you have deployed that you know “where to find the rainbow in your network”. That was done in the past with special hardware or TABs. The approach from the Big Switch Monitoring Fabric is to use standard whitebox switches for that with the BigSwitch Software on top. With the software based appoach you get a much more flexible TabNetwork that can be programmed via API and is capbale of Event triggered Monitoring. That wouldn´t be possible with only switches. BigSwitch introduced a new component witch they call Service Node. It is a x86 based server that uses DPDK in the backround to do all the magic that can not be proceded by a switch. The Big Monitoring Fabric is the first product that uses the Service node but I suggest in the Future all the really exciting new stuff from BigSwitch will be done with some kind of x86 servers that have more flexebilty from a software capability standpoint.
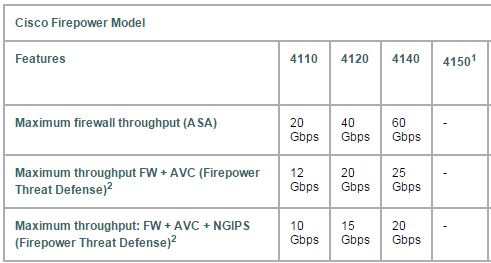
 Cisco has introduced at the Cisco Live the new FirePOWER 4100 device Family. besides a new Hardware Platform the really interesting development is going on the backround. First a short brief of the new 4100 appliances, they come out in 3 different versions at the start and a 4th model will be added in the 2nd half of 2016. It is a 1RU appliance that can do up to 20GB/s FW throughput with L7FW, AVC and IPS enabled.
Cisco has introduced at the Cisco Live the new FirePOWER 4100 device Family. besides a new Hardware Platform the really interesting development is going on the backround. First a short brief of the new 4100 appliances, they come out in 3 different versions at the start and a 4th model will be added in the 2nd half of 2016. It is a 1RU appliance that can do up to 20GB/s FW throughput with L7FW, AVC and IPS enabled.